This session explores data privacy laws and cyber security / privacy frameworks, and how to create a data security strategy. Learn key application security standards, how to identify business logic flaws in applications, and what’s required for threat modeling of new systems. Other topics include adopting security best practices such as secrets management, sensitive data detection using application security tools, and a holistic systems security engineering approach to mitigate against cyber-attacks.
With corporate data and applications moving to the cloud, the bring-your-own-devices (BYOD) paradigm, and growing adoption of remote work, the traditional security perimeter has disappeared. Organizations must now face the challenge of defining new security policies to mitigate the risks associated with a perimeterless network: sensitive data leakage, and data privacy and regulatory compliance breaches. In addition, data protection and privacy laws such as GDPR impose fines on organizations that don’t protect consumer data.
And cyber attackers are becoming more sophisticated. In the recent SolarWinds supply chain attack, attackers were able to subvert SolarWinds’ software development process and insert a malicious back door into its network monitoring software. This malware-infected software was digitally signed by the company and propagated to 18,000 customers via the software update process, and that gave hackers access to sensitive corporate and personal data. This clearly underscores the need for companies to be more vigilant in how they handle legitimate and certified software in their supply chain from trusted vendors.
Organizations that develop commercial software or procure software from third-party vendors also need to better secure their internal software development workflows, as well as expand their software acceptance criteria. Using the right security tools (e.g., endpoint and network detection/monitoring/response, and privileged access management), as well as deploying application security tools and services across the entire software development life cycle, will help better secure commercial software and applications.
Find out more at InfoSec Belgium from Anna Chiang on April 1 at 10.30am.
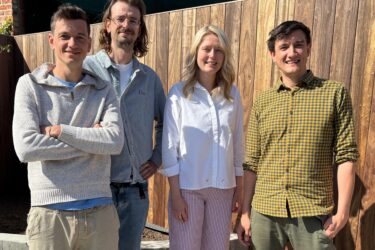
Anna Chiang leads go-to-market activities for application security products. Prior to Synopsys, she worked at WhiteHat Security, Perforce Software, and BlackBerry where she drove product marketing efforts for AppSec and UEBA security products, as well as platform product management for enterprise and mobile application solutions. Chiang is a Certified Information Systems Security Professional (CISSP), with an EECS degree from U.C. Berkeley and a graduate degree in management from Stanford University.